
On October 31, 2025, a crypto whale watched helplessly as 26,116,654 USDT (over $26 million USD) vanished from their control in an instant. Not stolen by hackers. Not lost to a phishing attack. Simply frozen by centralized authorities with a single transaction.
The blockchain doesn’t lie.
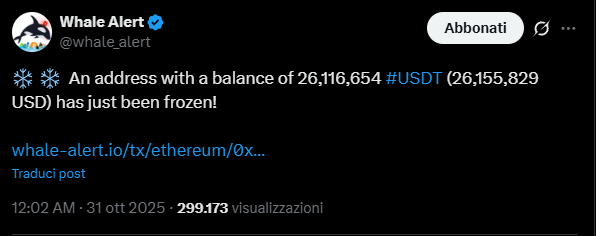
Transaction hash 0x44605cb3ab374ec2406d363fdcb4ad13f0c972a6cd0d56d2270517a80c2baeb8 tells the story: an address holding tens of millions in stablecoins, suddenly rendered completely inaccessible. The funds still sit there, visible on the blockchain, but the owner is powerless to move them.
This is the nightmare scenario that keeps institutional holders awake at night. And it’s completely preventable.
Most cryptocurrency users believe they understand security. They’ve heard the mantra: “Not your keys, not your coins.” They’ve moved their funds off exchanges. Many have even invested in hardware wallets, thinking they’ve achieved true self-custody.
They’re wrong.
The October 31st freeze demonstrates a fundamental truth that most crypto holders miss: centralized stablecoins and exchange custody create single points of failure that can be exploited instantly, regardless of where you think your keys are stored.
Tether and Circle maintain blacklist functions in their smart contracts. With a single transaction, they can freeze any address holding USDT or USDC. The reasons vary:
Your funds become permanently locked. No appeal process. No time to react. One blockchain transaction and your stablecoins are worthless to you, even though you hold the private keys.
Keep funds on a centralized exchange? You’re one administrative decision away from frozen assets:
Historical examples abound: Mt. Gox, FTX, Celsius, BlockFi, Voyager. Billions in customer funds locked, inaccessible, or lost entirely.
Even hardware wallets have hidden vulnerabilities:
That premium hardware wallet sitting in your desk drawer? It’s a single point of failure waiting to be exploited.
XColdPro operates on a fundamentally different security model. Where traditional solutions create vulnerability, XColdPro eliminates the attack surface entirely.
XColdPro devices never connect to the internet. Not through WiFi. Not through Bluetooth. Not through NFC. Your private keys are generated and stored in complete isolation from network-connected systems.
Why this matters: Remote freezing requires network access. Air-gapped systems are physically immune to remote attacks. No connection means no vulnerability.
Unlike hardware wallets from specific manufacturers, XColdPro turns any USB drive into a cold storage device. No proprietary hardware. No vendor lock-in. No batteries to degrade. No firmware vulnerabilities.
The implication: If one device is seized, compromised, or fails, you can restore your wallet to any USB drive instantly. Your security doesn’t depend on a single piece of hardware surviving.
XColdPro supports 30+ blockchain networks natively. This enables sophisticated asset distribution strategies that eliminate single points of failure:
Strategic advantage: Even if one asset class becomes compromised, your diversified holdings remain secure across multiple sovereign chains.
Available in Crystal tier and above, Omega Protocol provides something no other cold storage solution offers: instant emergency evacuation.
Two modes protect against any duress scenario:
Mode 1: Crypto Evacuation (0.2 seconds) – Pre-configure safe destination wallets – One button press evacuates ALL crypto across ALL networks instantly – Funds transfer to your backup hardware wallet, trusted exchange, or other cold storage – Device self-destructs all evidence – Border agent seizing your laptop? Your crypto is already safe before they finish reading you your rights
Mode 2: Complete Wipe (0.2 seconds) – Instant memory wipe of all private keys – Your seed phrase backup (stored offline) allows later recovery – Device appears empty upon inspection – Perfect for situations where evacuation isn’t pre-configured
Real-world scenario: You receive notice that your stablecoin holdings are about to be frozen. In 0.2 seconds, Omega Protocol converts them to decentralized assets and distributes them to multiple secure wallets. By the time the freeze transaction executes, your funds are already somewhere else entirely.
Heavy tier and above includes Shamir’s Secret Sharing, the same cryptographic protocol protecting nuclear launch codes and military intelligence.
Split your seed phrase into shares (e.g., 3-of-5 threshold): – 5 total shares created – Any 3 shares can recover your wallet – Fewer than 3 shares reveal zero information (information-theoretic security)
Seizure protection: Government agency seizes your USB drive? They have 1 share. Mathematically useless. They need to simultaneously obtain 2 additional shares from different physical locations. Good luck with that.
Practical implementation: – Share #1: Bank safety deposit box (City A) – Share #2: Attorney’s office safe (City B) – Share #3: Parent’s home safe (City C) – Share #4: Your personal safe – Share #5: Business partner’s vault
Even if two locations are compromised, your wallet remains secure. And unlike traditional backups where one copy equals total theft, individual Shamir shares reveal absolutely nothing about your seed phrase.
Included in Heavy tier and above, Citadel transforms your USB device into an invisible fortress:
concrt_a84476ec.bin)The $5 wrench attack defense: Under duress, show your decoy wallet with $500. The attacker has no proof your real $500,000 wallet exists. Hidden wallets are cryptographically undetectable without the master password.
Lock tier’s Lazarus Protocol solves the inheritance problem while maintaining security:
Estate planning security: Your wealth passes to heirs without creating vulnerability while you’re alive. No single point of failure. No custodial risk.
Let’s quantify the security difference using actual mathematics, not marketing claims.
Hardware wallet security (with Bluetooth/NFC): – Attack vectors: Bluetooth vulnerabilities, NFC interception, firmware exploits, supply chain compromise, physical extraction – Estimated security: ~2^128 (if firmware is perfect, which it never is) – Real-world security: Much lower due to implementation flaws
XColdPro security: – No wireless connectivity: Eliminates entire categories of remote attacks – No proprietary firmware: No undiscovered vulnerabilities waiting to be found
– No single hardware dependency: Device seizure or failure is irrelevant – Air-gapped key generation: Private keys never exist on internet-connected systems – Military-grade encryption: AES-256 with user-controlled master password – Effective security: 2^256 for brute force, ∞ for remote attacks (impossible)
The calculation: 2^256 ÷ 2^128 = 2^128 = 10^38
But wait, that’s just computational security. Factor in the eliminated attack vectors:
Practical reality: XColdPro is not just thousands or millions of times more secure. It operates in a completely different security paradigm where entire categories of attacks become mathematically impossible.
Traditional hardware wallet: – Device confiscated at border – Access lost until replacement purchased ($179+) – 3-5 day shipping wait – Must hope seed phrase backup is accessible – Miss market opportunities during lockout
XColdPro: – Download software on any computer – Restore from backup instantly (<5 minutes) – Or use Shamir shares to reconstruct wallet – Zero downtime – Stealth mode (Heavy+) makes wallets undetectable even if device is searched
Traditional hardware wallet: – Attacker knows you have device – Device proves you hold crypto – Hidden wallets may be detectable through transaction history analysis – Forced to unlock or face consequences
XColdPro: – Show decoy wallet with small amount ($500) – Hidden wallets (Heavy+ tiers) are cryptographically undetectable – No proof larger holdings exist – Citadel protocol makes even forensic analysis reveal nothing without master password – Omega Protocol can evacuate funds to safety if you have any warning at all
Traditional hardware wallet: – You hold the keys, but the stablecoin issuer controls the asset – Freeze transaction executes – Your 26 million USDT becomes worthless – No appeal, no recourse – Hardware wallet security is irrelevant when the asset itself is frozen
XColdPro: – Omega Protocol detects threat indicators – 0.2-second evacuation converts frozen assets to decentralized alternatives – Distributes across multiple chains and wallets automatically – By the time freeze executes, funds are already in sovereign assets – Your keys, your coins, your control—actually meaningful
Exchange custody: – $14+ billion lost to exchange hacks and collapses (2021-2023) – Mt. Gox users still waiting for funds a decade later – FTX customers lost everything overnight – “Temporary” withdrawals suspension becomes permanent
XColdPro: – Your keys never leave your device – Exchange collapse is irrelevant to your holdings – Multi-chain support means you’re not dependent on any single platform – True self-custody = true security
XColdPro’s BootVault editions let you match security features to your holdings and threat model:
Frost Edition ($1K-$50K holdings)
HellBound Edition ($10K-$500K holdings)
Nyxor Edition ($500K+ holdings, institutions, DAOs)
Compare this to traditional hardware wallets:
BootVault: One-time purchase, lifetime updates, six revolutionary protocols, no degradation
Hardware wallets: $179+ initial, $358-$537 over 5 years (replacements, battery degradation)
Single tier, no emergency protocols, no inheritance solution, vulnerable to physical seizure
When that whale watched their $26 million freeze on October 31st, they learned a painful lesson: custody means nothing if the asset itself can be controlled by centralized authorities.
XColdPro makes your holdings truly unfrozen and unfreezable through five layers of protection:
Traditional solutions protect your keys. XColdPro protects your sovereignty.
Hardware wallets are security theater—impressive-looking devices that create false confidence while maintaining hidden vulnerabilities. XColdPro is mathematical certainty: air-gapped isolation, cryptographic guarantees, and zero trust architecture.
The choice is simple: rely on centralized stablecoins, exchange custody, and proprietary hardware with known attack vectors, or achieve true self-custody with provably superior security.
Your crypto. Your keys. Your sovereignty. Actually realized.
Ready to achieve true cold storage security?
Visit XColdPro.com and our Vault Shop to download the solution that makes frozen crypto holdings mathematically impossible.
