3 min read
| Time to Hack: Attack Surface: Persistence: Network Exposure: Key Extraction Methods: Successful Hacks: Recovery Rate: | Physically impossible when USB removed 0 bytes on host system None – runs entirely in RAM 0% (USB-only execution) Physical USB theft only 0 (new product) 100% with mnemonic |
THE LAST WALLET YOU’LL EVER NEED
Security Architecture
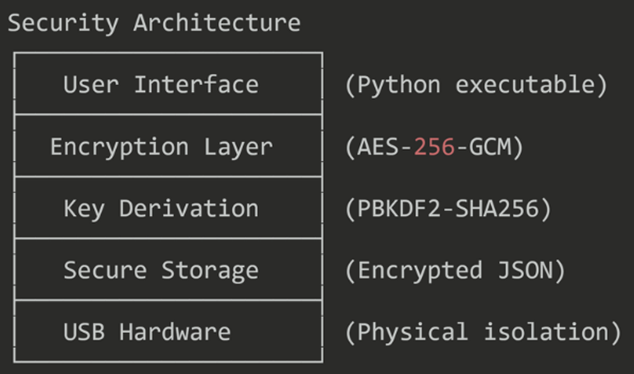
This layered design ensures that each stage of interaction—from interface to storage—operates under independent cryptographic protections.
Ever wondered how strong your ColdGuardian and BootVault software really are? Let’s break it down with some real-world math:
Total Combined Entropy: well over 512 bits of effective cryptographic strength.
✅ Fun takeaway: By the time someone brute-forces your ColdGuardian, the universe will have gone cold, dark, and silent.
High-end desktop (RTX 5090-class + AES-NI CPU)
Even granting an optimistic 1×10⁹ key guesses/second for raw AES-256:
A maxed-out gaming/workstation PC can’t make a dent. Memory-hard KDFs (like scrypt) multiply the pain by orders of magnitude.
Grover’s algorithm gives a square-root speed-up, so AES-256 ~ 2¹²⁸ work in principle. But current quantum machines are nowhere near the qubits, fidelity, or error-correction required.
Even if you imagine a wildly generous 10¹² iterations/sec quantum box:
With today’s (and foreseeable) quantum hardware, AES-256 remains far beyond reach. Grover reduces the exponent, not the problem.
